Crypto and cybersecurity sit at a crossroads of trust, code, and governance. The field demands risk-aware, transparent practices that map attackers’ tactics to layered defenses. Detail-oriented governance, auditable decision-making, and continual monitoring anchor secure wallets, exchanges, and contracts while preserving user autonomy. As policy, incident response, and independent verification shape resilience, new tensions emerge between innovation and protection. The stakes are high, and crucial choices await those who must balance security with open systems.
What Is the Intersection of Crypto and Cybersecurity?
The intersection of crypto and cybersecurity sits at the confluence of decentralized systems, cryptographic protocols, and the safeguarding of digital assets. This domain emphasizes cryptography governance, ensuring accountability and transparent decision-making.
It also centers on crypto risk assessment, evaluating threats, controls, and resilience. Stakeholders pursue resilient architectures while preserving freedom, security, and auditable governance in dynamic, interoperable networks.
How Attackers Exploit Crypto Systems and How to Defend
How do attackers exploit crypto systems, and what defenses map to resilient governance? Detected gaps enable bypass methods as threat actors target weak controls, governance risk, and audit trails. Social engineering shapes access routes, emphasizing human factors alongside cryptographic flaws. Defenses prioritize transparent risk governance, layered authentication, incident playbooks, independent verification, and continuous monitoring to deter exploitation while preserving user autonomy.
Practical Security Practices for Wallets, Exchanges, and Contracts
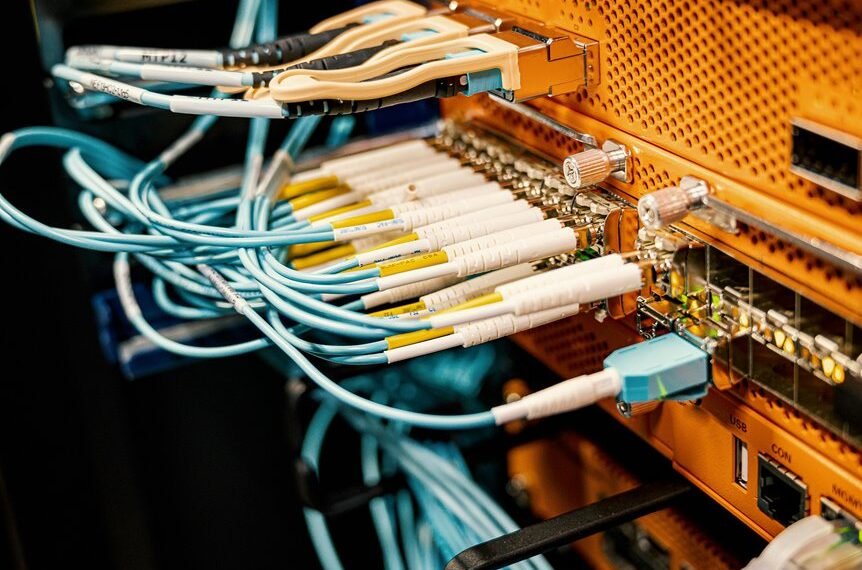
In practical security practices for wallets, exchanges, and contracts, organizations must balance usability with rigorous controls, recognizing that weak authentication, mismanaged keys, and insecure smart contract code create systemic risk across the ecosystem.
Data privacy and key management underpin governance, demanding proactive threat modeling, formal review, and auditable processes to minimize exposure while preserving user autonomy, transparency, and freedom to innovate securely.
Navigating Policy, Governance, and Incident Response in Crypto Security
The discussion emphasizes policy governance frameworks, accountability, and transparent decision-making.
It highlights incident response readiness, commensurate with risk, regulatory reporting, and post-incident lessons.
This stance balances risk awareness with governance discipline, empowering responsible innovation while safeguarding stakeholder trust in dynamic markets.
Frequently Asked Questions
How Do Quantum Computers Threaten Current Cryptographic Standards?
Quantum computers threaten current cryptographic standards by potentially breaking widely used public-key schemes; governance must anticipate this with quantum resistance strategies and post quantum crypto, ensuring risk-aware, freedom-preserving transition plans for resilient, interoperable systems.
What Are Common Social Engineering Risks in Crypto Platforms?
Common social engineering risks in crypto platforms include phishing, fake support, and misleading contracts. The analysis emphasizes phishing awareness, governance controls, and mitigation plans; a risk-aware stance supports user freedom while implementing layered verification and incident response protocols.
Can Hardware Wallets Protect Against Supply Chain Attacks?
Coincidence suggests hardware wallets and cold storage mitigate some supply-chain compromises, yet reliance on chain integrity, node operators, and blockchain analytics remains essential; governance-aware practices balance security with personal freedom in risk-aware, detail-oriented stewardship.
See also: mediajio
How Do Rug Pulls Differ From Exit Scams in Defi?
Rug pulls exploit project developers’ deceit, while exit scams involve fraudulent liquidity withdrawals or platform abandonment; both undermine user funds, demanding robust governance, transparent audits, and risk-aware stewardship to protect freedom and ensure accountability within decentralized ecosystems.
What Are Best Practices for Individual Privacy With Crypto?
One third of crypto users—about 33%—prioritize privacy, highlighting a trend toward safeguards. The guidance emphasizes privacy auditing and personal data minimization, framed by risk-aware governance: protect liberties while enabling compliant, transparent, freedom-centered financial activity.
Conclusion
In the crucible where crypto meets cybersecurity, risk is a constant companion and governance a steady compass. The ecosystem thrives only when transparent threat models, auditable decisions, and layered defenses align with user autonomy. Defenders map adversaries, regulators set guardrails, and developers fortify code, wallets, and contracts with disciplined rigor. The horizon remains perilous but navigable: resilience grows where accountability, continuous monitoring, and prudent innovation intersect, guiding stakeholders toward secure, inclusive, and enduring digital assets.